Advanced 5G

Capture new opportunities with Advanced 5G
The new opportunities and potential of Advanced 5G are incredibly exciting.
Our Advanced 5G solutions are focusing on what matters most to our customers:
- Enhanced 5G performance from a network KPI and end customer experience standpoint.
- Support for new service revenues and new end-to-end network capabilities.
- Driving down costs with efficient and sustainable use of resources.
- Leveraging AI across the network to further enhance intelligent and autonomous operations.
Advanced 5G is built on the foundation of existing 5G network investments.
5G has been the fastest deployed radio access network generation so far, with projected annual data growth of 20-30%.
AI is already driving down mobile network costs and will bring further efficiencies for Advanced 5G.
Build your path to Advanced 5G
Our Advanced 5G solutions are built upon a foundation of existing 5G network investments to deliver greater performance and resource efficiency. They can drive down network costs and provide a platform to launch and support a wealth of new monetization opportunities.
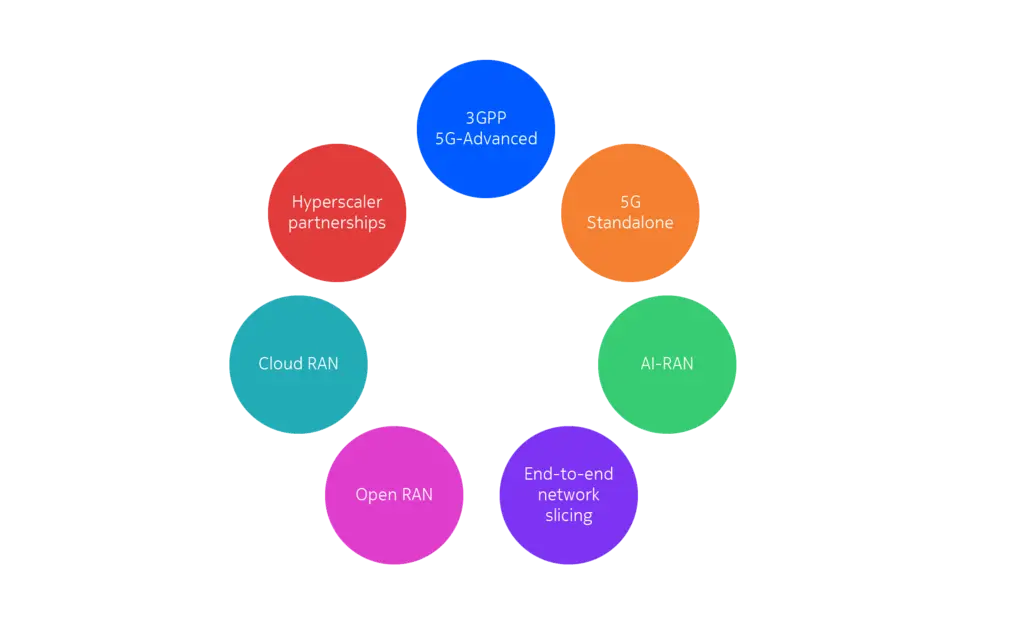
Along with 3GPP developments, Advanced 5G is complemented by areas such as 5G RAN disaggregation, cloudification and all-encompassing AI capabilities. With a 5G Standalone architecture, Advanced 5G enables enhanced capabilities such as end-to-end slicing and open API gateways.
We provide maximum flexibility and consistency to our customers, regardless of what combination of solutions they choose to implement on the path to Advanced 5G. This allows mobile network operators to be assured of investment performance with the ability to gradually scale aspects of Advanced 5G across their network.
Enhance 5G performance
Mobile network performance is often benchmarked in crowdsourced measurements, by independent research companies and operators themselves. Factors that influence performance include uplink and downlink data rates, latency, mobility, packet loss, coverage, consistency and availability. These are measured through test use cases covering voice, file downloads, browsing and gaming. In the near future, they are likely to include extended reality and other immersive services.
All these measures are important as they reflect end customer’s quality of experience.
In maximizing network performance, our Advanced 5G solutions evolve with feature support in areas such as:
High order uplink and downlink carrier aggregation for superior throughput.
Low latency, low loss, scalable throughput (L4S) for prioritizing real-time traffic in congested cells.
Uplink boost and coverage enhancements.
AI-driven autonomous RAN performance optimizations and AI-based services.
Another factor that influences end-customer perception of service is the battery life of their device. Smartphones need to support increasingly high processing loads, while IoT devices and wearables often need to manage small data packets on a low power budget.
Our Advanced 5G solutions address these requirements with innovative approaches such as refined extended discontinuous reception (eDRX), data reception in device low power states and studies into using low power wake-up signal/receivers.
With our Advanced 5G solutions, we will help you enhance end-user experience and differentiate with performance
Carrier aggregation
Combine with advanced Beamforming algorithms and Massive MIMO techniques for superior throughput.
Low latency, low loss, scalable throughput (L4S)
- Based on pioneering research by Nokia Bell Labs.
- Monetize Quality of Service (QoS) differentiation.
Uplink coverage boost
- Enable seamless user experience also in challenging cell-edge conditions.
- Extend battery life of end-user devices.
AI-driven optimizations
- Simplify operations.
- Maximize performance.
- Optimize energy efficiency.
- Minimize operational costs.
Capture new revenue streams
New Advanced 5G capabilities supported by flexible network architectures will deliver new revenues while enabling increased resource efficiency and lower costs. In many cases, 5G Standalone is required to support these new revenue-generating services.
End-to-end slicing
Service-aware, intent-driven networks
RedCap
5G low-bandwidth solution with lower cost devices.
Extended reality
Untethered XR experiences.
Precise positioning
Location-based services.
As 5G networks evolve toward a multi-purpose computing platform, AI-RAN and cloudification will open new opportunities for service revenues. For example, through APIs and programmability, operators can offer RAN-specific information to augment AI applications. AI and RAN will benefit from platform synergies for offering enriched application performance.
Drive down operational costs
Our Advanced 5G solutions help drive down operational costs with intelligent, efficient and sustainable use of resources.
Spectral efficiency
Support for features such as Multi-User MIMO (MU-MIMO) and advanced Beamforming algorithms help increase spectral efficiency and cell load capabilities, driving down the cost per traffic unit.
Operational efficiency
Already today, our AI-driven solutions and services optimize performance and reduce manual effort with autonomous operations. With Advanced 5G, we will further enhance our AI capabilities
Energy efficiency
RAN energy consumption remains a huge focus for both cost and sustainability efforts. Our solutions optimize energy efficiency based on network traffic and enable AI-driven energy management.
Amplify your knowledge

Triangulates – Growing business with Advanced 5G
This episode discusses the impact of Advanced 5G on network performance, monetization and energy efficiency, and the role of AI.

Triangulates - RedCap
This episode explores 5G RedCap, the low-bandwidth solution that expands the 5G ecosystem with new industrial and consumer devices.

Triangulates - Maximizing 5G performance
Don't miss our Triangulates session: Maximizing 5G performance.

Triangulates - 5G Standalone
The steps needed today to unlock the many benefits of 5G Standalone and enable the future evolution of radio networks.

5G-Advanced standards
3GPP Standardization: Enhancing 5G capabilities and paving the path to 6G.
Nokia Tech Winter Horizon
Watch our Tech Winter Horizon event with industry perspectives on AI-RAN.

Nokia subscription center
Subscribe to marketing communications from Nokia.
More questions?
Learn more

Blog

Blog
Event series
Video
Nokia & SFR power network performance and sustainability

Event

White paper

White paper

Event
Latest news
Please complete the form below.
The form is loading, please wait...
Thank you. We have received your inquiry. Please continue browsing.