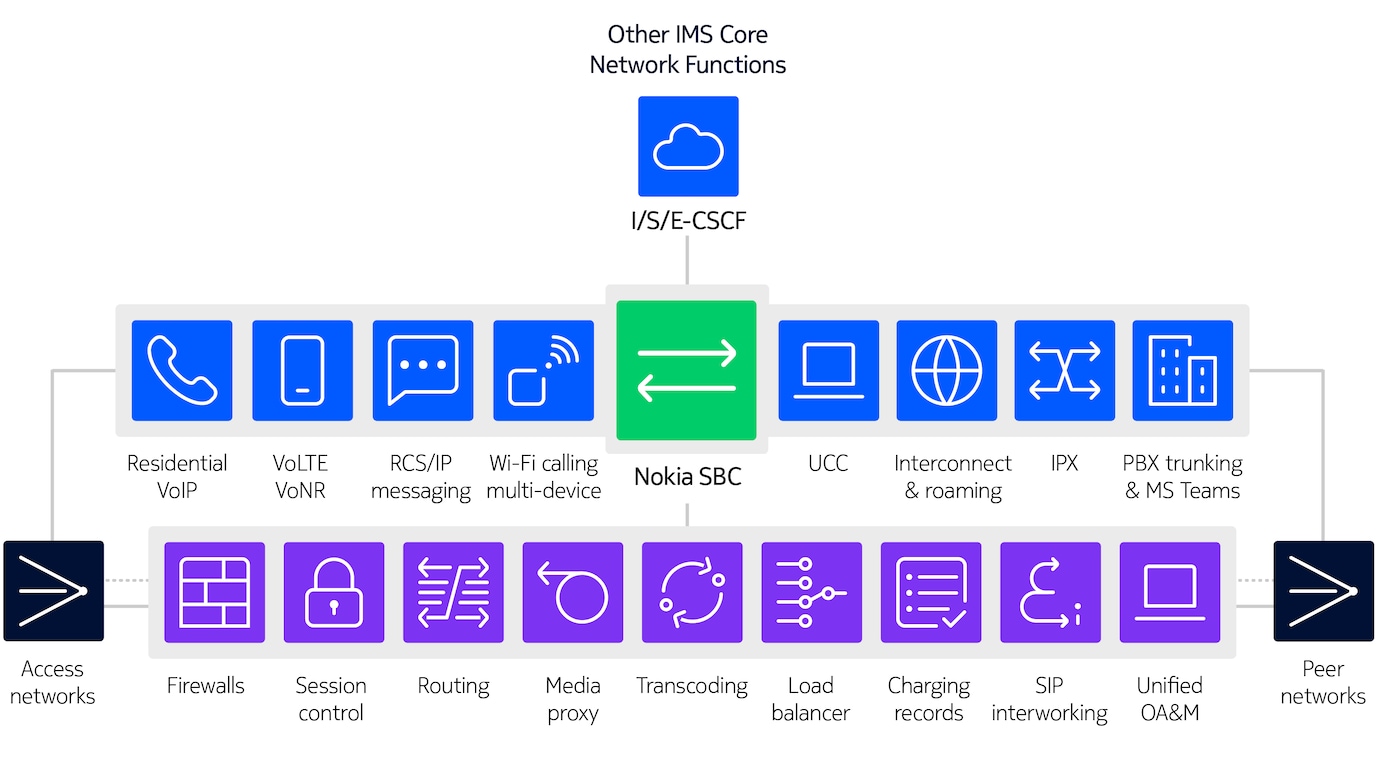
Nokia Session Border Controller (SBC) secures signaling and control media crossing the edges of the IMS network.
Nokia SBC sits at the edge of the access networks to secure any type of IP accesses and deliver all IMS services. It also sits on the edge of the peering networks to support roaming, IMS interconnection or corporate SIP trunking scenario.
The challenges facing service providers
The landscape of CSPs providing IMS services is changing
VoLTE deployment continues, replacing 2G and 3G circuit switched networks across the globe. 227 operators have launched commercial VoLTE service in 109 countries1. VoLTE based on IMS is also required to provide voice services in 5G networks.
This creates new CSP challenges in scaling mobile networks, interconnect and roaming with other carriers, and with operations and analytics for these networks.
1 Source: GSMA, Evolution from 4G to 5G, January 2022
IP based multimedia services are critical infrastructure
Today more than ever, every aspect of our lives and businesses depend on IP-based communications. Further, these services are experiencing increased numbers and severity of cyberattacks.
The CSP faces challenges of IMS interoperability and network protection from non-compliant and misbehaving devices, scaling for massive IoT and 5G bandwidth, access and peering edge cyberattacks, and a requirement to guard against “insider” security and privacy attacks.
SBC is moving to the cloud
Networks are transitioning to the cloud, and this includes the SBC. This drives a focus on the SBC media plane, especially for transcoding and encryption since these are computationally intensive bearer plane functions. It is also important to consider how to move SBC to move to containerized microservices on public and hybrid cloud architectures.
What does a Session Border Controller (SBC) do?
The session border controller typically provides the following functions for the IMS network:
- Encryption/decryption of bearer traffic
- Firewall and topology hiding for security
- Media handling and transcoding
- SIP interworking
- NAT traversal
Nokia’s SBC can be deployed as a standalone SBC or as part of Nokia’s VoLTE/VoWiFi solution.
SBC for Fixed VoIP
For VoIP services provided to residential and enterprise customers, the SBC provides DoS/DDoS protection, topology hiding of the network from the access, NAT traversal, and CODEC support for G.729, G.722, & T.38 Fax.
SBC for PBX Trunking
The carrier’s SBC secures and controls access from IP-PBXs, supporting VLANs, managing overlapping IP addresses, surrogate registration, and performs media release.
SBC for VoLTE
In a VoLTE core network, the SBC controls access and allows mobility. It provides an EVS CODEC, and supports eSRVCC, VoWiFi, NPLI, S8HR roaming, and provides the network access interface for voice services on 5G networks.
SBC for Enterprise unified communications
The SBC in the carrier network secures connections to interconnect enterprises (or government networks). It provides Microsoft Teams Direct Routing allowing MS Teams access from off network phones, and hosted PBX connections.
SBC for Peering
The SBC provides a secure interconnection between service providers with a centralized routing function, intelligent transcoding, SIP-I interworking, and call admission control (CAC).
SBC for Home assistants
The SBC secures access from home assistant services (e.g. Google Home Assistant). It provides support for ICE Lite, the Opus CODEC, and enables web authentication.
Why choose Nokia for your session border controller?
Flexible architecture
The right architectural fit, on the right infrastructure, with one software load for all applications
Cloud optimized
Virtual networking and data plane acceleration for high performance using a cloud-native architecture
Operational simplification
Simplified life cycle management with consistent OA&M and CI/CD deployment
Secure all services
Comprehensive protection across access and peering policies and protocols
Network analytics
SLA verification, QoE assurance, and troubleshooting
Resources
Datasheets
Related solutions and products
Product
How to scale your Policy Control Function for 4G and 5G with the Nokia Policy Controller
Service
Quickly realize foundational core network services
Learn more about core networks and voice core

Article
Blog

Article

Blog

Video
Video
Nokia Core TV series #33: Digital twin for optimizing CNF configurations

Customer success

Customer success
Please complete the form below.
The form is loading, please wait...
Thank you. We have received your inquiry. Please continue browsing.