NetGuard Certificate Lifecycle Manager
Automate the lifecycle management of your security certificates
What is NetGuard Certificate Lifecycle Manager (NCLM)?
Secure automated certificate lifecycle management for Nokia SOAR
NetGuard Certificate Lifecycle Manager (NCLM) is a comprehensive solution for the certificate lifecycle management of digital identities. NCLM automates the enrollment, renewal, and deployment of public keys and certificates in a centralized, secure and cost-effective way, preventing costly outages and vulnerabilities.
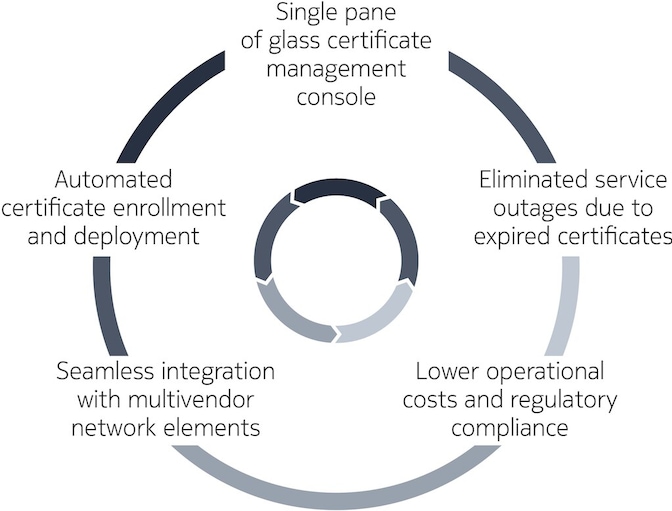
Benefits of NetGuard Certificate Lifecycle Manager
- It offers full visibility to the deployed certificate base.
- It improves network security posture by reducing risks arising from outdated or rogue digital identities.
- It improves reliability by eliminating service outages due to expired certificates and lowers operational costs through enhanced automation.

Data sheet
NetGuard Certificate Lifecycle Manager
The role of digital certificates in certificate lifecycle management
Digital certificates are the most common method for both users and machines to secure communication, authentication and authorization in proven technologies. Enterprises, communication service providers, cloud service providers, and IoT device manufacturers are using certificates as a fundamental building block within their security infrastructure.
Outcomes of expired digital certificates in certificate lifecycle management
Weak certificates cause costly outages and eavesdropping
Expired certificates can easily lead to costly outages and downtime. While weak and poorly-configured certificates can be used to hijack connections, eavesdrop on network traffic, or manipulate application data.

White paper
The need for digital certificates in 5G networks
NCLM addresses these issues and gives security and cybersecurity operations teams full control over their certificate lifecycle management processes. It allows for seamless integration between various public certification authorities (CAs), such as Entrust, Symantec, or Digicert. In addition support for enterprise PKIs, such as Microsoft CA, Insta Certifier, or Nokia’s NetGuard Certificate Manager.
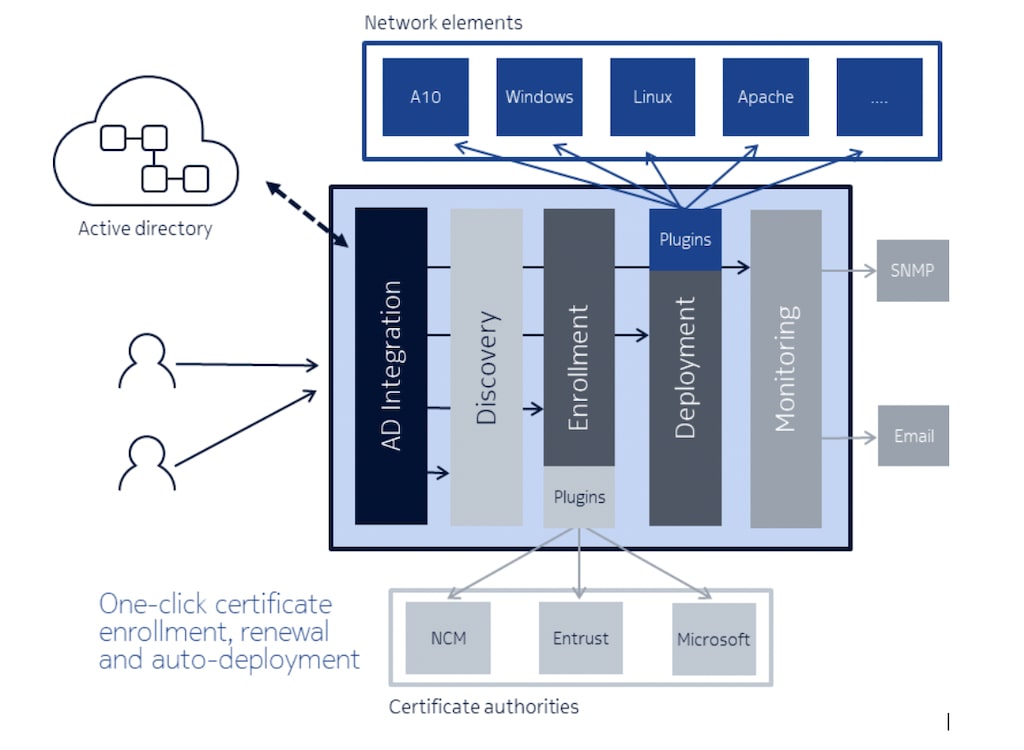
How does NCLM work? Unified certificate management with NCLM
NCLM is an agnostic solution and provides unified management of every single certificate regardless of the issuing source. It uses an open platform that supports plug-ins, enabling seamless integration with multivendor network elements and devices for centralized, single-step certificate deployment.
Benefits and features of Nokia Certificate Lifecycle Manager
Enrollment in certificate lifecycle management: Enroll and renew a certificate on behalf of the target system
- Key pair management (generation and deletion)
- Certificate enrollment and renewal from different certification authorities via a plugin-based mechanism – Supported CAs: MS-CA, Entrust,NCM
- Certificate browsing and filtering
- Manual PKCS#12 import
- Template functionality to pre-populate certificate attributes or enrollment parameters
- Domain/FQDN whitelisting
Deployment in certificate lifecycle management: Deploy and install certificates to a target system
- Configuration of deploy mechanism via plugin-based mechanism
- Automated or manual certificate and key installation and activation
- Deployment templates to pre-populate deployment parameters
Monitoring and validation in certificate lifecycle management: Enables control of certificate deployment and certificate correctness
- Status view of certificate enrollment and deployment
- Certificate search and filter capabilities
- Customizable email notification for certificate expiry and revocation status
- Granular reporting and alerting
- Customizable certificate metadata for enhanced asset management
- GUI-based log viewer • Workflow-based certificate enrollment and deployment
- Certificate benchmarking against “gold standard”
Certificate lifecycle management discovery: Ability to scan network ranges for SSL/TSL enabled devices and discover certificate-based services
- Network scans based on IP addresses or IP ranges
- Service scanning and identification
- Automatic import into NCLM for further certificate management
- Email notification and reporting
Active directory integration: Simplified management of PKI users and groups from Microsoft Active Directory
- Active Directory group-based access mapping to target system groups or systems
- Definition of granular access permissions (i.g. read-only, read-write, access to private key) based on user roles
- Role-based access to enrollment and deployment plugin configuration
- “Need to know” principle
Resources
Datasheets
White papers
Related solutions and products
Solution
Cloud-native Extended Detection and Response
Product
Automate the audit and analysis of all parameters in physical and virtual networks
Product
Digital identity management with secured and standardized PK
Product
5G cybersecurity orchestration and incident response software suite to detect, analyze, and mitigate telco security risks faster.
Product
Designed for mission critical infrastructures.
Product
Secure physical or virtual networks with Privileged Access Management (PAM)
Learn more about security

Article

Blog

Blog
Blog

Blog

Blog
eBook

Article
Latest news
Please complete the form below.
The form is loading, please wait...
Thank you. We have received your inquiry. Please continue browsing.