IP network security
Protect your network with multi-layered embedded IP network security
Our growing global digital economy, cloud architectures, 5G, and continuing digital transformation are opening the door to a new generation of network-level attacks and security threats that target IP networks and the data that flows across them. Current solutions lack the scale and functionality to address the growing threat volume and complexity.
At Nokia, we embed security into every layer of our IP network infrastructure. We deliver the at-scale, fully featured protection you need to guarantee the performance and integrity of your mission critical networks.
Threat Intelligence Report in 2024
Identifying attack trends to protect telecom networks and customers
Why must we build secure IP networks
IP networks are changing faster than ever. With these changes come new network-level security threats and a broader attack surface:
- Increasing numbers of IoT and Industry 4.0 devices are being connected to the IP network and may be vulnerable to hijacking. Once hijacked, these devices have access to wide bandwidth to launch attacks.
- Service providers and enterprises are embracing third party transport options, open network architectures and globalization. This makes their networks increasingly porous, and the data they transport increasingly vulnerable to confidentiality and integrity breaches.
- Our digital economy, digital transformation, and technologies such as 5G are accelerating cloudification, which enables network functions and services to run anywhere. As network functions become more distributed, the attack surface increases.
As the attack surface grows, so does the frequency, scale, and potency of the attacks themselves:
- Millions of hijacked IoT devices are used to create DDoS botnets that flood networks with terabits of data and hundreds of millions of packets per second. A new generation of threats aims to use shorter and more sophisticated multi-vector attacks to disrupt networks, making it harder to be detected and stopped. And, whether these impactful, volumetric DDoS attacks target the IP network infrastructure belonging to CSPs or use it to reach another target – possibly beyond their networks - they impair the CSP's ability to maintain consistently high quality of services and customers’ connectivity.
- As quantum computers grow more powerful, they will inevitably compromise today's public key cryptography (Q-Day) and expose the sensitive data. Harvest now and decrypt later (HNDL) activity, combined with the timeline to evolve to Quantum-Safe cryptography, is accelerating this exposure by placing today's data at risk.
Threat impacts are escalating
The threat from man-in-the-middle attacks and data breaches are also escalating. Enterprises embracing digitalization are concerned about loss of intellectual property, revenue, and reputation. Governments are concerned at the potential national security implications and growing disruption of critical infrastructure and services that may have societal and economic impact. Service providers looking to secure potential new revenue from the digitalization of government, research and education and other critical industries must be able to demonstrate that data flowing across their networks is impervious to these threat vectors.
Addressing all these network-level threats is difficult for security solutions that run on top of IP networks. They lack the cost-effective scale and functionality to fully protect IP networks from the growing threat landscape.

eBook
Build a self-defending secure IP Network
Multilayer embedded IP network security is a new imperative in the evolution of mission-critical networks.
We secure IP networks from within
To provide at-scale protection of IP networks, IP network security must be like packet forwarding – a high-performance, highly scalable capability of the IP network itself.
Nokia has pioneered this approach by embedding security into the DNA of every layer of our IP network infrastructure, providing high-performance, fully featured and at-scale protection for your mission-critical IP networks.
Adopt a multi-layered approach to IP network security
Our multi-layer embedded approach to IP network security begins at the IP silicon layer. Our FP silicon provides the filtering scale and performance headroom necessary to be a highly precise attack sensor and mitigation element. Integrated MACsec and ANYsec secured with AES-256 network encryption, delivers highly scalable (1G-800G) secure network connectivity. Both capabilities can be used at line rate – without impacting the performance of other services running on the same chipset. This ensures network performance and service quality remain high even during the most intense DDoS attacks.
While our network operating systems (NOS), deliver both platform security and trust to protect against a range of potential system level attacks, including unauthorized access, control plane targeting, vulnerability exploitation. Our platform trust is anchored around the pillars of system integrity verification and system encryption.
At the tools and applications layer, our integrated, high-performance IPsec gateway (Nokia Secure Gateway) inherits the scale, resiliency, and security of the carrier-grade 7750 SR infrastructure. A single Nokia Secure Gateway can support up to 32,000 base stations and up to 3.2Tbps of encrypted traffic.
Our Nokia SR OS Firewall protects the integrity of the control and management planes between trusted zones, while our carrier grade network address translation (CG-NAT) delivers the scale and performance for our customers to protect the identity and security of their subscribers.
When it comes to observability and security, our Deepfield Genome data feeds provide comprehensive internet-wide traffic flow and distributed denial of service (DDoS) security insights to help you better understand the traffic that passes across their network – from the internet to end-users, and equip you to better protect your network, services, and customers from DDoS attacks. Deepfield Defender provides multi-dimensional security intelligence, analytics, and automation that can empower your IP network infrastructure to quickly identify and self-mitigate DDoS attacks.
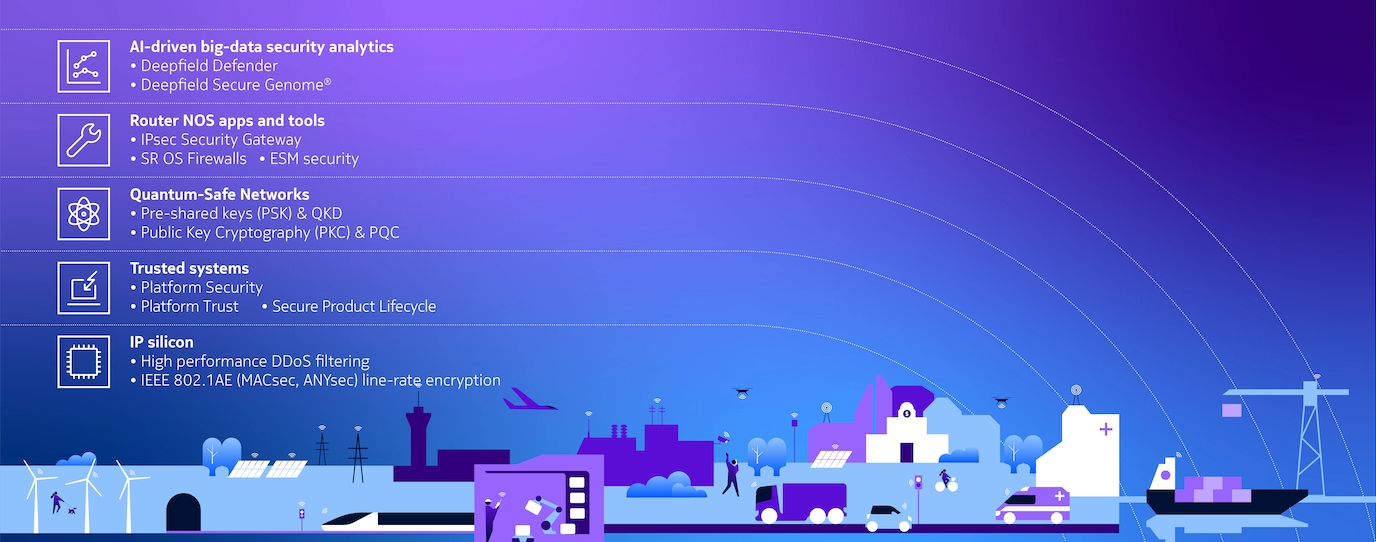
Diagram representing Nokia's multi-layer approach to built-in network security
Quantum-Safe Networks
Delivering quantum-safe connectivity demands a comprehensive strategy. Nokia Quantum-Safe Networks have a defense-in-depth approach that delivers Quantum-Safe security at multiple layers through multi-layered cryptography, that can adapt to your business needs, give you the confidence to scale Quantum-Safe IP networks, but can also evolve with the quantum landscape
Integration with the 1830 Security Management Server (SMS) enables centralized pre-shared key (PSK) management across both the Nokia IP and optical network portfolios, and the ability to leverage quantum-based keys with Quantum Key Distribution (QKD).
Our FP (FP5 and FPcx) silicon extends our Quantum-Safe IEEE 802.1 AE MACsec implementation, to provide Quantum-Safe ANYsec. This extends the low latency and simplicity of MACsec encryption to tunnels, flows and slices engineered using MPLS, Segment Routing and IP.
Nokia's MACsec/ANYsec implementation provides you with the freedom to transform IP services into Quantum-Safe IP services on demand by turning on encryption whenever and wherever it is required. This can be done natively no matter what service or network transport is being used, and without impacting the performance of any other service running on the same chipset.
Identify and mitigate attacks automatically
Using manual solutions and forensic analysis, you can’t respond quickly enough to stop attacks from causing disruption, and accuracy is sometimes compromised.
Nokia Deepfield Defender and 7750 SR and 7730 SXR series routers allow you to identify and respond to attacks automatically. Security policies are continuously monitored and tuned using telemetry from the network. With the automated workflows in Deepfield Defender, you can update tens of thousands of IP silicon filters in seconds to respond to changing security conditions without delay.
Accuracy is high. High-scale, highly granular filters can inspect IP headers or use signature matching to identify and mitigate against sophisticated attacks without impacting router performance. Deepfield Defender adds multi-dimensional security analytics, giving you unprecedented insight into DDoS attacks of all types. The telemetry information obtained from the network is combined with Deepfield Secure Genome, allowing Defender to obtain unique visibility into internet traffic and security and to minimize the impact on the network, services, and customers.
With Nokia, you can block attacks with greater precision before they impact service quality.
Protect everything, everywhere, all the time
Due to the prohibitive cost and limited scale of traditional DDoS solutions, CSPs have only been able to protect a few select customers or a portion of their network from DDoS attacks.
With IP security embedded within the network, you can protect your whole network and all your customers, all the time. Deepfield Defender and 7750 SR and 7730 SXR series routers shield you from all types of attacks (such as botnet, multi-vector, spoofing, or carpet bombing), from any origin (inbound or outbound), towards any target (not just protected targets), on any boundary (core, peering, data center, or service edge).
By stopping all customer-directed attacks at the edge of your network, service quality and network performance always remain high.
It’s about protecting your brand and business: customers want a network that won’t let them down and providing one will help to reduce churn.
White paper
The future mode of DDoS attack mitigation
Explore related topics
Related solutions and products
Product
A next-generation platform for DDoS mitigation
Product
High-performance IP edge and core routers.
Product
Deepfield Defender by Nokia provides advanced AI-driven DDoS detection and mitigation, enabling real-time protection at scale with great cost-efficiency.
Product
Keep your customers’ IP traffic quantum-safe in the quantum era
Learn more about IP networks and security

Blog

Blog

Blog

Customer success

Topic

Blog

Blog

Application note
Latest news
Please complete the form below.
The form is loading, please wait...
Thank you. We have received your inquiry. Please continue browsing.
At-scale protection for mission-critical IP networks
Let’s discuss how our unique approach to IP network security delivers the protection you need to guarantee the performance and integrity of your mission-critical IP networks.





