When runtime security plays by telecom rules

Telecom attacks increasingly favor persistence over disruption. They blend into normal operations, remain invisible under periodic inspection, and surface only when impact is already external – a service incident, a regulator’s question, a board‑level escalation.
By that point, the window for controlled response is narrow.
Detecting this kind of behavior earlier pulls security into service‑bearing network functions, where it has to live with the same constraints as everything else that keeps the network running: availability, performance, predictability. If runtime security cannot operate safely inside those limits, it stops reducing risk and starts creating it.
For telecom leaders, this turns runtime security into a network architecture decision, one with direct consequences for service continuity, regulatory confidence, and the long‑term cost of operating high‑performance networks.
Continuous runtime behavior, observed as it happens
Runtime security needs to see how network functions behave while they execute, not how they appear at isolated points in time. Many malicious actions in telecom networks appear unremarkable when seen individually. Intent only becomes visible when those actions are connected and observed in sequence.
Following behavior as it unfolds preserves that context: how processes are invoked, how communication evolves, how actions relate to one another during normal operation. It allows gradual deviation to be distinguished from legitimate variability, while services remain live.
AI‑driven detection depends on this continuity. When visibility is fragmented, low‑noise attacks simply merge into background activity, because no single moment looks suspicious on its own.
Security that is safe to run in telecom networks
In telecom environments, security has to be safe by construction.
Nothing is added to individual workloads. Execution paths stay exactly as they were and traffic flows exactly as before, preserving expected service behavior under live load. There are no per‑CNF agents, no sidecars, no changes to application images, and no modifications to service chains. Observation happens without inserting logic into workload execution or packet handling.
Runtime security is not tied to CNF build, deployment, or upgrade workflows. It is managed at the platform level, aligned with the host and kernel lifecycles that network functions already inherit.
The same discipline applies to resources. Monitoring shares CPU, memory and scheduling with latency‑sensitive workloads. If its behavior cannot remain bounded and stable under peak traffic, it is not safe to deploy in a telecom network.
eBPF engineered for telecom constraints
One important dimension of runtime visibility comes from kernel‑level insight. Applied with discipline, Extended Berkeley Packet Filter (eBPF) acts as a non-intrusive agent that enables continuous observation of processes, system calls and execution context without modifying kernel state or execution paths.
That continuous view establishes a baseline for expected behavior. When execution follows those paths, activity remains normal. When it doesn’t, deviations surface immediately, without waiting for reconstruction or secondary indicators.
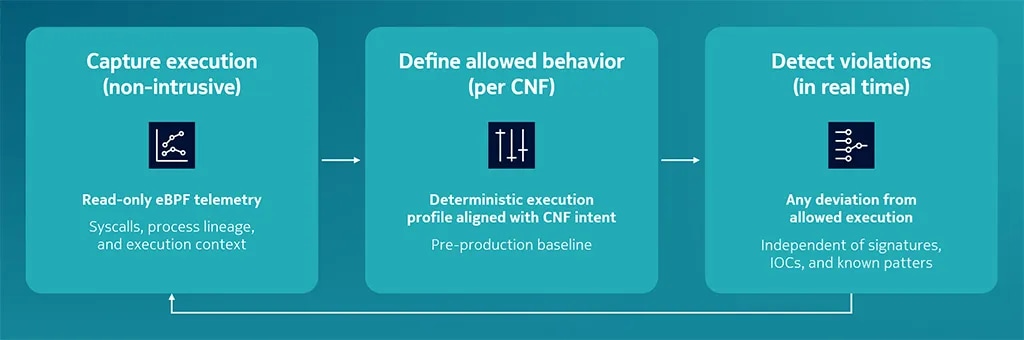
Image: eBPF-based microservice behavior analysis in NetGuard EDR
Safety depends on how eBPF is applied. Signal capture is intentionally narrow, limited to security‑relevant kernel events. Evaluation and response are handled in user space, keeping kernel execution paths read‑only, bounded and predictable.
This discipline avoids the instability risks historically associated with in‑kernel security logic, which is an essential condition for sustaining five‑nines availability in core network functions.
When runtime security stays within these limits, telecom providers gain earlier detection without increasing outage risk, avoid repeated certification cycles, and reduce the operational cost of securing live networks.
Platform trust across telecom lifecycles
Kernel‑level instrumentation is part of the attack surface. While attackers have shown how kernel tooling can be abused for persistence or stealth, telecom‑grade runtime security cannot assume trust by default.
In Nokia NetGuard Endpoint Detection and Response, eBPF probes are observation‑only by design. They are delivered as signed images, loaded under restricted Linux capabilities, and validated by the in‑kernel BPF verifier on every load, ensuring kernel state and execution paths remain unchanged throughout their lifecycle.
Telecom platforms evolve slowly and deliberately. Kernel upgrades are staged, versions coexist, and validation cycles are long. Security that requires frequent rebuilds or tight coupling to specific kernel versions increases operational risk and governance overhead.
Compile Once, Run Everywhere allows the same instrumentation to work across kernel versions, reducing repeated certification and re‑validation cycles in regulated, multi‑vendor telecom environments.
Runtime signals in a layered detection system
Even normal activity inside network functions can hide malicious intent. Interpreting that behavior requires visibility deep inside telecom applications, while they are running.
At that depth, runtime visibility operates under the same constraints as the applications themselves. Those constraints strictly bound how intrusive any probe can be – and, by design, how much it can safely observe.
For that reason, eBPF supplies kernel‑level signals into the AI‑driven detection pipeline. In NetGuard EDR, those signals are combined with network‑function telemetry and traffic sensor data to form reliable security events, allowing AI-driven detection to reason across layers without inserting logic into packet paths.
That boundary defines effective runtime security in telecom networks.
Inside it, detection strengthens resilience.
Beyond it, security becomes an operational risk.


