Co-location information of devices, people, and activities can be used in numerous applications in areas of social networking, mobile networking, spatial and socio-economics, and securing interacti
We propose a low-overhead scheme for detecting a network partition or cut in a sensor network. Consider a network S of n sensors, modeled as points in a two-dimensional plane.
Finding telecommunications fraud in masses of call records is more difficult than finding a needle in a haystack.
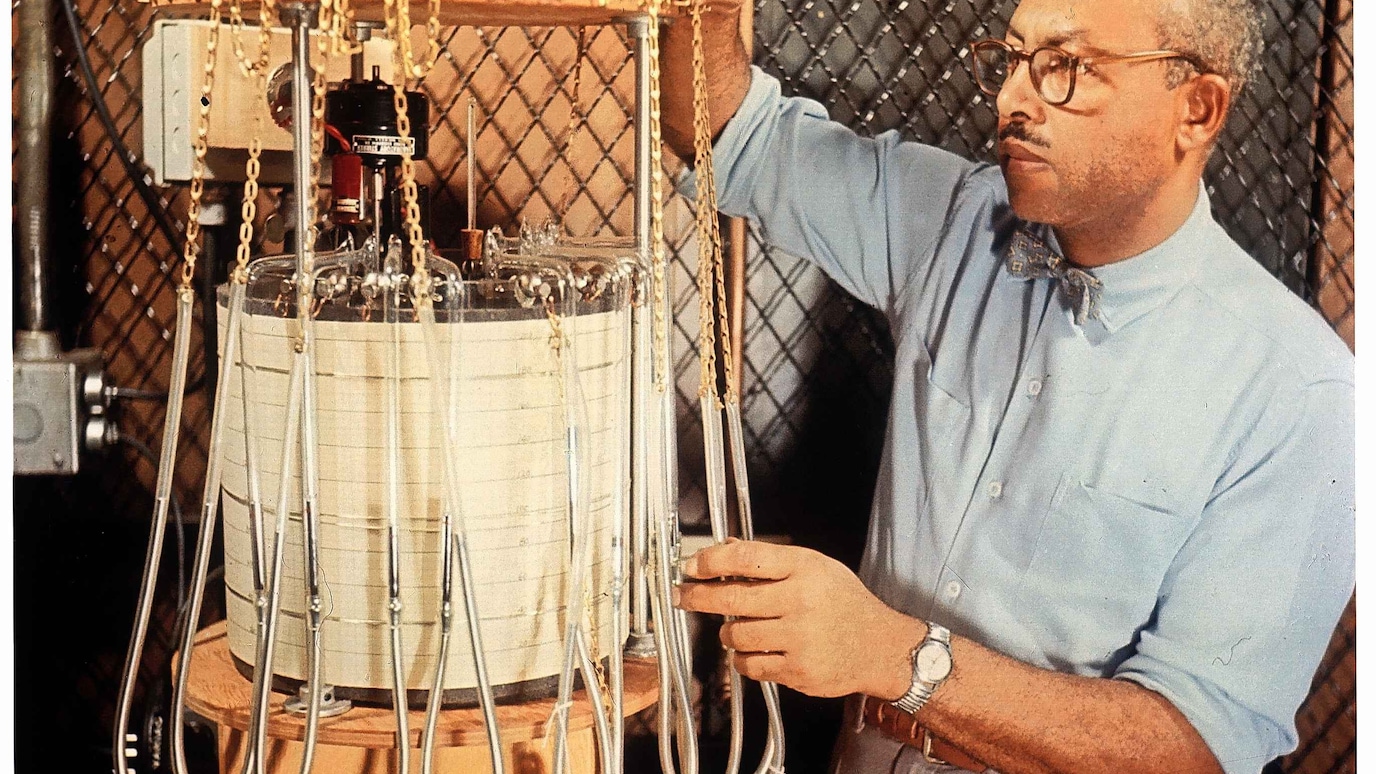
The free oscillations of the earth appear as decaying sinusoids in low frequency seismic records.
In this paper, we consider the problem of detecting an intruding packet in a communication network.
We present a multiple taper method for detecting nonstationaty signals in a time series based on a statistical test that measures the confidence one can assign to a signal's existence at any given
The popularity of Twitter greatly depends on the quality and integrity of the contents contributed by users.
In condensed matter there are many boson fields which, like light, can be driven into a squeezed state through anharmonic interactions with an intense pump.
We consider the problem of implementing a detector for stop consonants in continuously spoken speech.
The theory of frequency modulation has always been beset by analytical difficulties, and nowhere have these been more in evidence than in the area of optimal demodulation of noisy FM signals.
Explore more
Video
AI-enhance wireless reliability: joint source and channel coding for robust 6G air interface
Blog
Blog
Podcast