Breaking a botnet DDoS "Enigma" code

Call me old-fashioned, but I only cheer for the good guys. Always. You know, Kate and Steve from Line of Duty, and any and all blue teams, such as the one from Blue Lights.
But there is one blue team that makes me especially proud – the team that keeps the internet and telecommunications service providers' networks safe and secure, and communications humming. It's the Nokia Deepfield Emergency Response Team (ERT) - the team of human defenders behind our AI-powered Deepfield Defender and our ERT support service.
So, let me tell you a recent story about how the Nokia Deepfield Emergency Response Team unraveled a network of hijacked devices capable of knocking almost anything offline (as much as I can share here). First, they found one DDoS cyberweapon. And then, four more.
Something wicked this way comes
As Craig Labovitz, Head of Technology at Nokia Deepfield, alluded to in his LinkedIn post, we have entered a whole new era of Distributed Denial of Service (DDoS) attacks that began in the second half of 2025 - a major transition from enterprise botnet to residential proxy DDoS. The image below shows a sample of attacks from February 2025 to February 2026, with each circle representing an individual attack. The data for the image comes from Deepfield Secure Genome® and from Deepfield customers participating in the Nokia Deepfield Global DDoS Threat Alliance (GDTA).
If all you see is red, your vision is OK. Most impactful DDoS attacks today are driven by residential proxies. We talked about this in our 2025 Nokia Threat Intelligence Report. But we did not expect to see that 33 Tbps DDoS attacks (or higher) would become this frequent in such a short time.
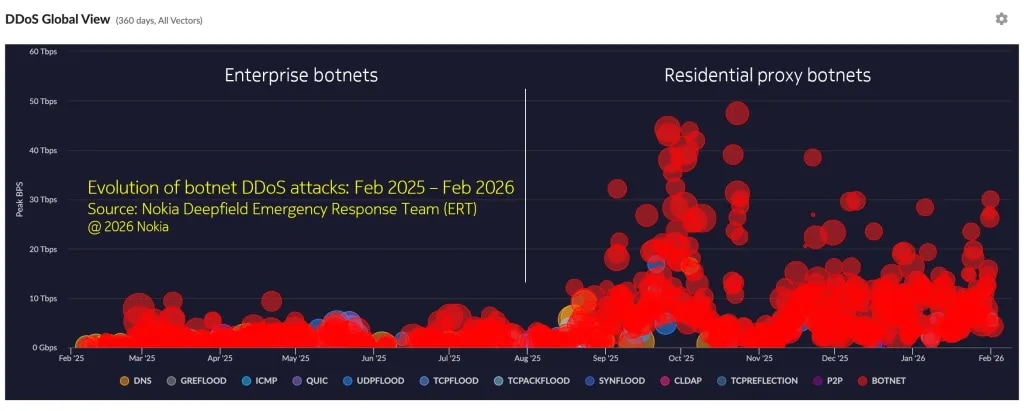
Figure 1. Evolution of DDoS attacks by peak volume (in bps), February 2025 to February 2026
Preventing Code Blue for the internet: ERT to the rescue
When my colleagues, security researchers at the Nokia Deepfield ERT, began investigating a wave of record-breaking cyberattacks that began last year, they expected to find a single criminal operation.
Instead, they found five — working together, sharing tools, and designed so that shutting down any single one would leave the others untouched.
The findings, which we publish at https://github.com/deepfield/public-research/, include our full report on the Aisuru ecosystem, published last on March 20, by the Nokia Deepfield ERT, and timed to wait until a federal law enforcement action took place first.
In the past, we talked about an interconnected ecosystem of botnets — armies of hijacked consumer devices, from home routers to smart TVs to streaming boxes, commandeered without their owners' knowledge and weaponized to flood targets with DDoS traffic, overwhelming websites, banks, hospitals, internet providers, and government services, and rendering them unreachable.
The scale is staggering.
One of the botnets in the group, called Kimwolf, had compromised an estimated 1.8 million devices worldwide, according to separate research by XLab. Another, called Aisuru, was linked to some of the largest DDoS attacks ever recorded — traffic floods measured in the tens of terabits per second, volumes large enough to saturate the infrastructure of major internet service providers, and many small and moderate country-level networks worldwide.
Four of the five botnets have now been disrupted by federal authorities, according to a statement from the U.S. Department of Justice. (Our team got a nice "thank you" nod there).
Hiding in your living room
What makes these botnets particularly difficult to combat is where they live. The compromised devices are not servers in data centers. They are the everyday gadgets sitting in millions of homes: Wi-Fi routers, digital video recorders, Android-based TV boxes, and set-top devices sold by internet providers.
Most owners have no idea that their devices have been hijacked for malicious purposes. The malware runs silently in the background, waiting for instructions. When an attack order arrives, each device contributes a small stream of traffic. Multiplied across hundreds of thousands or millions of devices, the combined traffic volume can be devastating.
As my colleague Jérôme Meyer, a Security Researcher at Nokia Deepfield, tells me, "These are not sophisticated computers being hacked. These are cheap consumer devices with poor security, connected to home broadband. The sheer number of them, along with the gigabit and even multigigabit broadband connectivity now available to them, is what creates the threat."
The five botnets — known in the security community as Aisuru, Jackskid, Kimwolf, MossadProxy, and Cecilio — each target different types of devices using different methods. Aisuru exploits known software flaws in routers and video recorders. Jackskid tries common default passwords on devices that still accept remote logins. Kimwolf takes advantage of a residential proxy flaw, related to the area of consumer use where companies pay consumers to share their internet connections, but inadvertently leave a maintenance port exposed on millions of devices.) MossadProxy delivers its payload through the same exposed maintenance port on Android TV boxes.
Cecilio, the fifth, appears to be more loosely connected — built from different underlying code but sharing operational resources with the others.
Breaking a DDoS botnet "Enigma"
The Nokia Deepfield ERT's breakthrough came from a small but telling detail: a custom modification to an encryption algorithm used to hide each botnet's communications.
In the same way that a counterfeiter might use a distinctive paper stock or ink mixture that links otherwise different-looking bills to the same printing operation, the botnet developers had embedded a unique cryptographic signature in their code. When that same signature turned up in what appeared to be a completely unrelated botnet, the Deepfield ERT researchers realized they were looking at a single operation disguised as several independent ones.
"It was the equivalent of finding the same fingerprint at two different crime scenes that nobody thought were connected," said one member of the Deepfield ERT.
Further investigation revealed additional connections: shared password lists used to break into devices, overlapping server infrastructure, and — most strikingly — an identical sequence of 15 network port numbers, in the same order, embedded in the configurations of two supposedly unrelated botnets. The odds of that being coincidental are, as the Deepfield ERT noted in the report, the kind of evidence that does not require statistical analysis.
A DDoS whack-a-mole, powered by crypto and blockchain
The most alarming feature of this malicious ecosystem is its resilience. The five botnets use five entirely different methods to receive instructions from their operators — including conventional internet lookups, encrypted web traffic, records stored on the Ethereum blockchain, an alternative domain name system invisible to standard internet monitoring, and custom encrypted communication channels.
This means that even if law enforcement or internet providers manage to block one communication channel, the others continue operating. It is, as the Nokia researchers described it, "defense in depth — just not the kind we usually advocate for."
The use of blockchain technology is particularly concerning. One of the botnets stores its command server addresses on the Ethereum network — the same technology that underpins cryptocurrency and digital contracts. Because blockchain records are distributed across thousands of computers worldwide and cannot be altered without the operator's private cryptographic key, they are more resistant to the traditional law enforcement tool of seizing domain names.
AI-powered DDoS
In our 2025 Nokia Threat Intelligence Report, we discussed how AI technology has evolved to power serious threats to critical infrastructure.
Hospitals have been knocked offline during emergencies. Financial institutions have lost access to trading systems. Government services have been rendered unavailable during critical periods. DDoS-for-hire services, sometimes euphemistically marketed as "stress testing" tools, allow virtually anyone to purchase an attack for as little as a few dollars.
In their March 20 research, the Deepfield ERT identified ties between the botnet ecosystem and at least one such service marketed as "Rebirth."
Our Deepfield ERT also found that malicious and criminal operators behind these botnets appear to be using modern software development practices, including AI-assisted coding tools. A compiled artifact in one of the malware samples references Cursor, a popular AI-powered code editor, indicating that the people building these weapons are adopting the same productivity tools as legitimate software developers.
What consumers and telecommunications providers can do
Security experts agree that the most effective defense starts at home. Consumers should change default passwords on routers and connected devices, install firmware updates when available, and disable remote management features they do not actively use.
For internet service providers, telecommunications providers and enterprises, the Nokia Deepfield ERT's findings underscore the limitations of monitoring any single layer of network traffic. This DDoS ecosystem was deliberately designed to evade detection by spreading its communications across multiple protocols and platforms.
Modern DDoS defense and protection demand the latest advances in AI and machine learning — capabilities that can analyze vast volumes of network telemetry in real time, detect anomalous traffic patterns within seconds, and trigger surgical countermeasures before an attack peaks.
But technology alone is not enough.
Behind every effective defense is a blue team of seasoned security experts — analysts, network engineers, and incident responders — whose judgment, contextual awareness, and hard-won experience are what transform raw intelligence into decisive action. AI can process billions of data points and spot the needle in the haystack, but it still takes a team of expert humans to understand why that needle matters and what to do about it.
So, pick both your AI-powered DDoS defense and the blue team behind it – carefully.
The full technical details and indicators of compromise have been published on GitHub to help other security teams detect and block the botnets.
Follow our public research at https://github.com/deepfield/public-research.
For more information about our DDoS security solution, visit https://www.nokia.com/ip-networks/deepfield/defender/.